AWS Security Blog
Category: Advanced (300)
How to use the Secrets Store CSI Driver provider Amazon EKS add-on with Secrets Manager
In this post, we introduce the AWS provider for the Secrets Store CSI Driver, a new AWS Secrets Manager add-on for Amazon Elastic Kubernetes Service (Amazon EKS) that you can use to fetch secrets from Secrets Manager and parameters from AWS Systems Manager Parameter Store and mount them as files in Kubernetes pods. The add-on […]
Introducing guidelines for network scanning
Amazon Web Services (AWS) is introducing guidelines for network scanning of customer workloads. By following these guidelines, conforming scanners will collect more accurate data, minimize abuse reports, and help improve the security of the internet for everyone. Network scanning is a practice in modern IT environments that can be used for either legitimate security needs […]
How to update CRLs without public access using AWS Private CA
Certificates and the hierarchy of trust they create are the backbone of a secure infrastructure. AWS Private Certificate Authority is a highly available certificate authority (CA) that you can use to create private CA hierarchies, secure your applications and devices with private certificates, and manage certificate lifecycles. A certificate revocation list (CRL) is a file […]
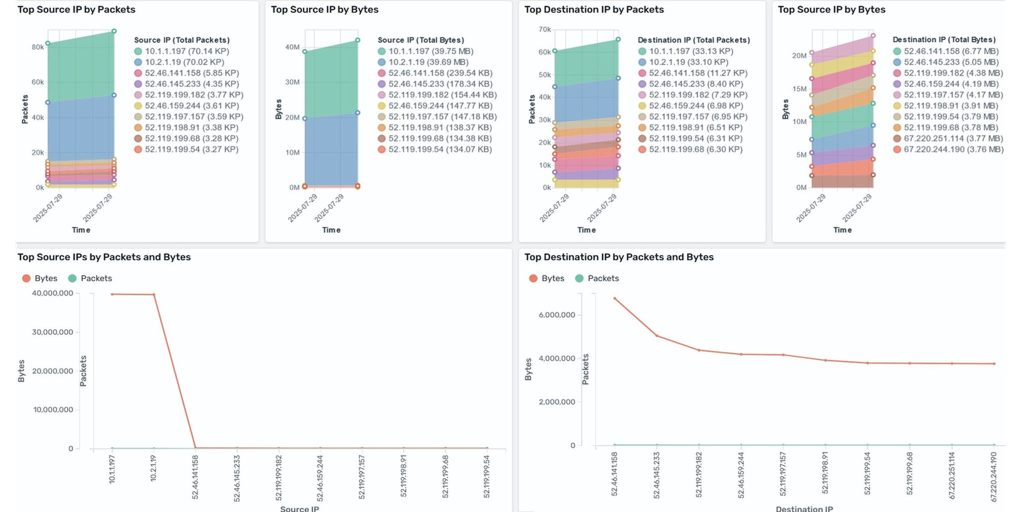
Analyze AWS Network Firewall logs using Amazon OpenSearch dashboard
Amazon CloudWatch and Amazon OpenSearch Service have launched a new dashboard that simplifies the analysis of AWS Network Firewall logs. Previously, in our blog post How to analyze AWS Network Firewall logs using Amazon OpenSearch Service we demonstrated the required services and steps to create an OpenSearch dashboard. The new dashboard removes these extra steps […]
Post-quantum (ML-DSA) code signing with AWS Private CA and AWS KMS
Following our recent announcement of ML-DSA support in AWS Key Management Service (AWS KMS), we just introduced post-quantum ML-DSA signature support in AWS Private Certificate Authority (AWS Private CA). Customers can use AWS Private CA to create and manage their own private public key infrastructure (PKI) hierarchies. Through this integration, you can establish and use […]
Migrating from Open Policy Agent to Amazon Verified Permissions
Application authorization is a critical component of modern software systems, determining what actions users can perform on specific resources. Many organizations have adopted Open Policy Agent (OPA) with its Rego policy language to implement fine-grained authorization controls across their applications and infrastructure. While OPA has proven effective for policy-as-code implementations, organizations are increasingly looking for […]
Using AWS Secrets Manager Agent with Amazon EKS
AWS Secrets Manager is a service that you can use to manage, retrieve, and rotate database credentials, application credentials, API keys, and other secrets throughout their lifecycles. You can also use Secrets Manager to replace hard-coded credentials in application source code with runtime calls to retrieve credentials dynamically when needed. Managing secrets in Amazon Elastic […]
Securing Amazon Bedrock API keys: Best practices for implementation and management
Recently, AWS released Amazon Bedrock API keys to make calls to the Amazon Bedrock API. In this post, we provide practical security guidance on effectively implementing, monitoring, and managing this new option for accessing Amazon Bedrock to help you build a comprehensive strategy for securing these keys. We also provide guidance on the larger family […]
Protect your generative AI applications against encoding-based attacks with Amazon Bedrock Guardrails
Amazon Bedrock Guardrails provides configurable safeguards to help you safely build generative AI applications at scale. It offers integrated safety and privacy protections that work across multiple foundation models (FMs), including models available in Amazon Bedrock and models hosted outside Amazon Bedrock from other providers. Bedrock Guardrails currently offers six key safeguards to help prevent […]
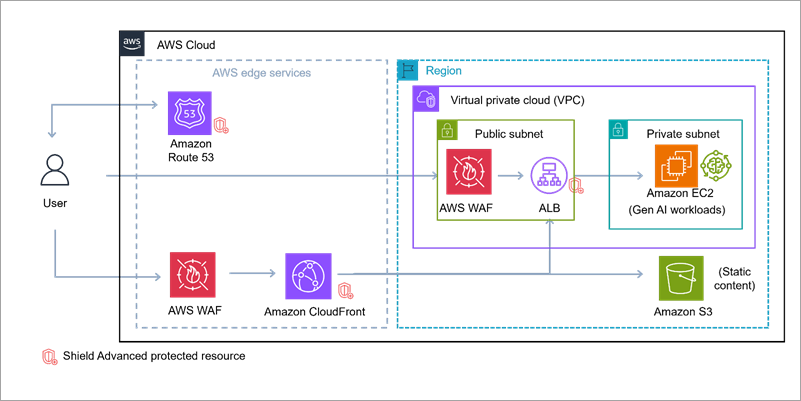
Build secure network architectures for generative AI applications using AWS services
As generative AI becomes foundational across industries—powering everything from conversational agents to real-time media synthesis—it simultaneously creates new opportunities for bad actors to exploit. The complex architectures behind generative AI applications expose a large surface area including public-facing APIs, inference services, custom web applications, and integrations with cloud infrastructure. These systems are not immune to […]