AWS Security Blog
Tag: AWS Organizations
How to automate AWS account creation with IAM Identity Center user assignment
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Background AWS Control Tower offers a straightforward way to set up and govern an Amazon Web Services (AWS) multi-account environment, following prescriptive best practices. […]
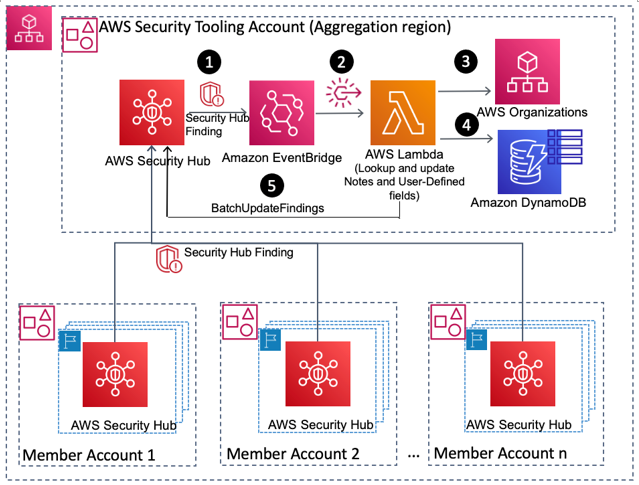
How to enrich AWS Security Hub findings with account metadata
In this blog post, we’ll walk you through how to deploy a solution to enrich AWS Security Hub findings with additional account-related metadata, such as the account name, the Organization Unit (OU) associated with the account, security contact information, and account tags. Account metadata can help you search findings, create insights, and better respond to […]
Simplify setup of Amazon Detective with AWS Organizations
Amazon Detective makes it easy to analyze, investigate, and quickly identify the root cause of potential security issues or suspicious activities by collecting log data from your AWS resources. Amazon Detective simplifies the process of a deep dive into a security finding from other AWS security services, such as Amazon GuardDuty and AWS SecurityHub. Detective […]
Enable Security Hub PCI DSS standard across your organization and disable specific controls
At this time, enabling the PCI DSS standard from within AWS Security Hub enables this compliance framework only within the Amazon Web Services (AWS) account you are presently administering. This blog post showcases a solution that can be used to customize the configuration and deployment of the PCI DSS standard compliance standard using AWS Security […]
How to restrict IAM roles to access AWS resources from specific geolocations using AWS Client VPN
You can improve your organization’s security posture by enforcing access to Amazon Web Services (AWS) resources based on IP address and geolocation. For example, users in your organization might bring their own devices, which might require additional security authorization checks and posture assessment in order to comply with corporate security requirements. Enforcing access to AWS […]
Highlights from the latest AWS Identity launches
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Here is the latest from AWS Identity from November 2020 through February 2021. The features highlighted in this blog post can help you manage […]
Use new account assignment APIs for AWS SSO to automate multi-account access
September 28, 2022: In July 2022, we renamed AWS Single Sign-On to AWS IAM Identity Center. In this blog, you will notice that we preserved backward compatibility with API calls and CLI scripts by retaining the API and CLI namespaces that were used under AWS Single Sign-On. September 12, 2022: This blog post has been […]
Control VPC sharing in an AWS multi-account setup with service control policies
January 29, 2021: We made minor updates to the architectural diagram in Figure 1. Amazon Web Services (AWS) customers who establish shared infrastructure services in a multi-account environment through AWS Organizations and AWS Resource Access Manager (RAM) may find that the default permissions assigned to the management account are too broad. This may allow organizational […]
Announcement: Availability of AWS recommendations for the management of AWS root account credentials
When AWS customers open their first account, they assume the responsibility for securely managing access to their root account credentials, under the Shared Responsibility Model. Initially protected by a password, it is the responsibility of each AWS customer to make decisions based on their operational and security requirements as to how they configure and manage […]
Securing resource tags used for authorization using a service control policy in AWS Organizations
In this post, I explain how you can use attribute-based access controls (ABAC) in Amazon Web Services (AWS) to help provision simple, maintainable access controls to different projects, teams, and workloads as your organization grows. ABAC gives you access to granular permissions and employee-attribute based authorization. By using ABAC, you need fewer AWS Identity and […]