AWS Security Blog
Automatically block suspicious traffic with AWS Network Firewall and Amazon GuardDuty
According to the AWS Security Incident Response Guide, by using security response automation, you can increase both the scale and the effectiveness of your security operations. Automation also helps you to adopt a more proactive approach to securing your workloads on AWS. For example, rather than spending time manually reacting to security alerts, you can […]
How to auto-remediate internet accessible ports with AWS Config and AWS Systems Manager
With the AWS Config service, you can assess, audit, and evaluate the configuration of your Amazon Web Services (AWS) resources. AWS Config continuously monitors and records your AWS resource configurations changes, and enables you to automate the evaluation of those recordings against desired configurations. Not only can AWS Config monitor and detect deviations from desired […]
How you can use Amazon GuardDuty to detect suspicious activity within your AWS account
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. Amazon GuardDuty is an automated threat detection service that continuously monitors for suspicious activity and unauthorized behavior to protect your AWS accounts, workloads, and data stored in Amazon S3. In this post, I’ll share how you can use GuardDuty with […]
Demystifying AWS KMS key operations, bring your own key (BYOK), custom key store, and ciphertext portability
October 4, 2024: This post has been updated to cover the following changes: FIPS 140-2 Level 3 validation of AWS Key Management Service (AWS KMS), the addition of the external key store service to AWS KMS, and FIPS 140-3 validation of AWS CloudHSM. As you prepare to build or migrate your workload on Amazon Web […]
Validate access to your S3 buckets before deploying permissions changes with IAM Access Analyzer
AWS Identity and Access Management (IAM) Access Analyzer helps you monitor and reduce access by using automated reasoning to generate comprehensive findings for resource access. Now, you can preview and validate public and cross-account access before deploying permission changes. For example, you can validate whether your S3 bucket would allow public access before deploying your […]
How to replicate secrets in AWS Secrets Manager to multiple Regions
On March 3, 2021, we launched a new feature for AWS Secrets Manager that makes it possible for you to replicate secrets across multiple AWS Regions. You can give your multi-Region applications access to replicated secrets in the required Regions and rely on Secrets Manager to keep the replicas in sync with the primary secret. […]
C5 Type 2 attestation report now available with one new Region and 123 services in scope
Amazon Web Services (AWS) is pleased to announce the issuance of the 2020 Cloud Computing Compliance Controls Catalogue (C5) Type 2 attestation report. We added one new AWS Region (Europe-Milan) and 21 additional services and service features to the scope of the 2020 report. Germany’s national cybersecurity authority, Bundesamt für Sicherheit in der Informationstechnik (BSI), […]
How AWS IAM Identity Center Active Directory sync enhances AWS application experiences
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. IAM Identity CenterIdentity management is easiest when you can manage identities in a centralized location and use these identities across various accounts and applications. […]
Essential security for everyone: Building a secure AWS foundation
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. In this post, I will show you how teams of all sizes can gain access to world-class security in the cloud without a dedicated […]
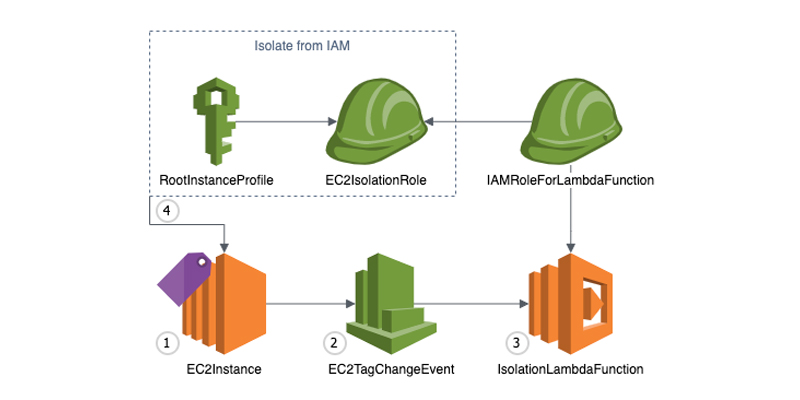
Automate Amazon EC2 instance isolation by using tags
Containment is a crucial part of an overall Incident Response Strategy, as this practice allows time for responders to perform forensics, eradication and recovery during an Incident. There are many different approaches to containment. In this post, we will be focusing on isolation—the ability to keep multiple targets separated so that each target only sees […]