AWS Security Blog
How to deploy AWS Network Firewall to help protect your network from malware
April 25, 2023: We’ve updated this blog post to include more security learning resources. Protecting your network and computers from security events requires multi-level strategies, and you can use network level traffic filtration as one level of defense. Users need access to the internet for business reasons, but they can inadvertently download malware, which can […]
How to automate AWS account creation with IAM Identity Center user assignment
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Background AWS Control Tower offers a straightforward way to set up and govern an Amazon Web Services (AWS) multi-account environment, following prescriptive best practices. […]
How to use tokenization to improve data security and reduce audit scope
April 25, 2023: We’ve updated this blog post to include more security learning resources. Tokenization of sensitive data elements is a hot topic, but you may not know what to tokenize, or even how to determine if tokenization is right for your organization’s business needs. Industries subject to financial, data security, regulatory, or privacy compliance […]
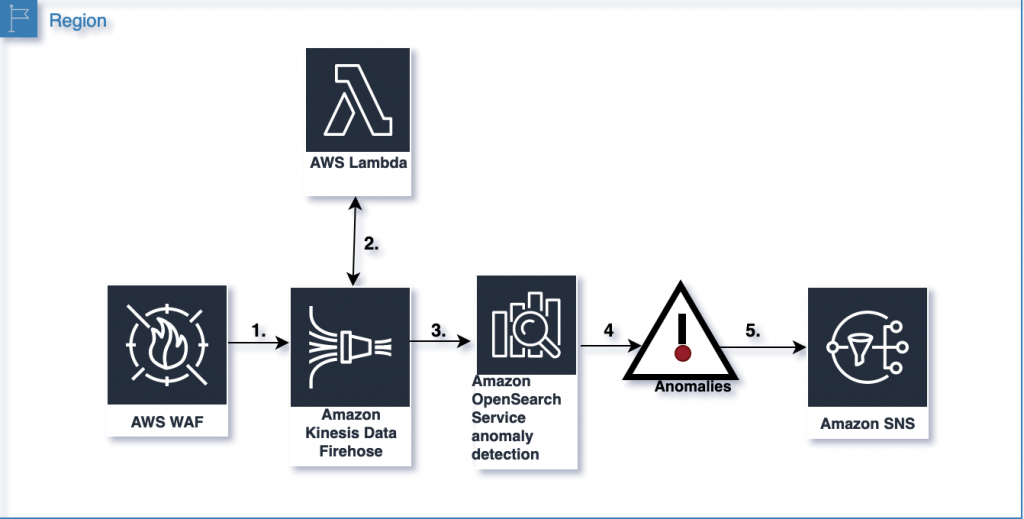
Analyze AWS WAF logs using Amazon OpenSearch Service anomaly detection built on Random Cut Forests
This blog post shows you how to use the machine learning capabilities of Amazon OpenSearch Service to detect and visualize anomalies in AWS WAF logs. AWS WAF logs are streamed to Amazon OpenSearch Service using Amazon Kinesis Data Firehose. Kinesis Data Firehose invokes an AWS Lambda function to transform incoming source data and deliver the […]
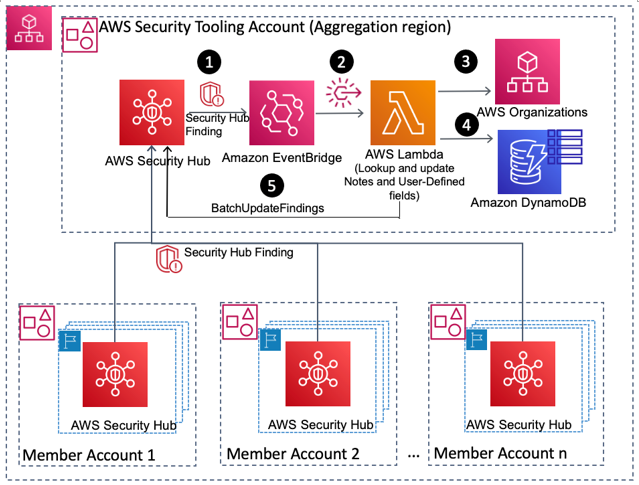
How to enrich AWS Security Hub findings with account metadata
In this blog post, we’ll walk you through how to deploy a solution to enrich AWS Security Hub findings with additional account-related metadata, such as the account name, the Organization Unit (OU) associated with the account, security contact information, and account tags. Account metadata can help you search findings, create insights, and better respond to […]
Fall 2021 PCI DSS report now available with 7 services added to compliance scope
We’re continuing to expand the scope of our assurance programs at Amazon Web Services (AWS) and are pleased to announce that seven new services have been added to the scope of our Payment Card Industry Data Security Standard (PCI DSS) certification. These new services provide our customers with more options to process and store their […]
Best practices for cross-Region aggregation of security findings
AWS Security Hub enables customers to have a centralized view into the security posture across their AWS environment by aggregating your security alerts from various AWS services and partner products in a standardized format so that you can more easily take action on them. To facilitate that central view, Security Hub allows you to designate […]
Continuous compliance monitoring using custom audit controls and frameworks with AWS Audit Manager
French version For most customers today, security compliance auditing can be a very cumbersome and costly process. This activity within a security program often comes with a dependency on third party audit firms and robust security teams, to periodically assess risk and raise compliance gaps aligned with applicable industry requirements. Due to the nature of […]
Top 10 security best practices for securing backups in AWS
Security is a shared responsibility between AWS and the customer. Customers have asked for ways to secure their backups in AWS. This post will guide you through a curated list of the top ten security best practices to secure your backup data and operations in AWS. While this blog post focuses on backup data and […]
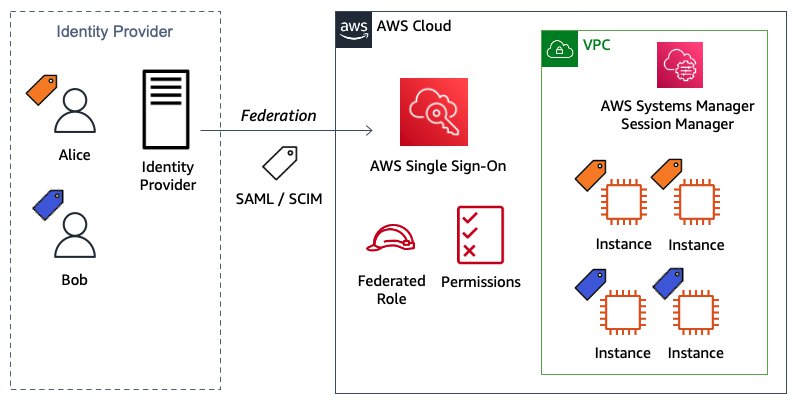
Configure AWS IAM Identity Center ABAC for EC2 instances and Systems Manager Session Manager
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. In this blog post, I show you how to configure AWS IAM Identity Center to define attribute-based access control (ABAC) permissions to manage Amazon […]