AWS Security Blog
Category: Advanced (300)
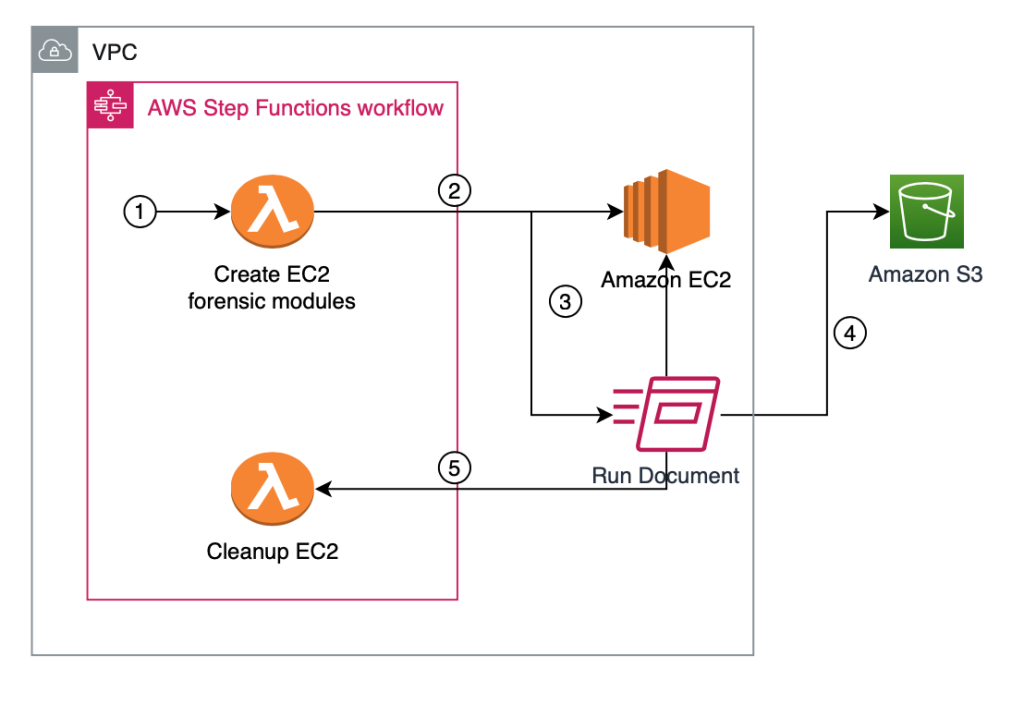
How to automatically build forensic kernel modules for Amazon Linux EC2 instances
In this blog post, we will walk you through the EC2 forensic module factory solution to deploy automation to build forensic kernel modules that are required for Amazon Elastic Compute Cloud (Amazon EC2) incident response automation. When an EC2 instance is suspected to have been compromised, it’s strongly recommended to investigate what happened to the […]
Implement step-up authentication with Amazon Cognito, Part 2: Deploy and test the solution
This solution consists of two parts. In the previous blog post Implement step-up authentication with Amazon Cognito, Part 1: Solution overview, you learned about the architecture and design of a step-up authentication solution that uses AWS services such as Amazon API Gateway, Amazon Cognito, Amazon DynamoDB, and AWS Lambda to protect privileged API operations. In […]
Implement step-up authentication with Amazon Cognito, Part 1: Solution overview
In this blog post, you’ll learn how to protect privileged business transactions that are exposed as APIs by using multi-factor authentication (MFA) or security challenges. These challenges have two components: what you know (such as passwords), and what you have (such as a one-time password token). By using these multi-factor security controls, you can implement […]
Scaling cross-account AWS KMS–encrypted Amazon S3 bucket access using ABAC
This blog post shows you how to share encrypted Amazon Simple Storage Service (Amazon S3) buckets across accounts on a multi-tenant data lake. Our objective is to show scalability over a larger volume of accounts that can access the data lake, in a scenario where there is one central account to share from. Most use […]
How to set up and track SLAs for resolving Security Hub findings
Your organization can use AWS Security Hub to gain a comprehensive view of your security and compliance posture across your Amazon Web Services (AWS) environment. Security Hub receives security findings from AWS security services and supported third-party products and centralizes them, providing a single view for identifying and analyzing security issues. Security Hub correlates findings […]
Identifying publicly accessible resources with Amazon VPC Network Access Analyzer
August 22, 2022: This post had been updated have the code fixed to make it easier for our readers to execute. Network and security teams often need to evaluate the internet accessibility of all their resources on AWS and block any non-essential internet access. Validating who has access to what can be complicated—there are several […]
How to detect suspicious activity in your AWS account by using private decoy resources
As customers mature their security posture on Amazon Web Services (AWS), they are adopting multiple ways to detect suspicious behavior and notify response teams or workflows to take action. One example is using Amazon GuardDuty to monitor AWS accounts and workloads for malicious activity and deliver detailed security findings for visibility and remediation. Another tactic […]
How to incorporate ACM PCA into your existing Windows Active Directory Certificate Services
Using certificates to authenticate and encrypt data is vital to any enterprise security. For example, companies rely on certificates to provide TLS encryption for web applications so that client data is protected. However, not all certificates need to be issued from a publicly trusted certificate authority (CA). A privately trusted CA can be leveraged to […]
Update of AWS Security Reference Architecture is now available
We’re happy to announce that an updated version of the AWS Security Reference Architecture (AWS SRA) is now available. The AWS SRA is a holistic set of guidelines for deploying the full complement of AWS security services in a multi-account environment. You can use it to help your organization to design, implement, and manage AWS […]
Automatically block suspicious DNS activity with Amazon GuardDuty and Route 53 Resolver DNS Firewall
In this blog post, we’ll show you how to use Amazon Route 53 Resolver DNS Firewall to automatically respond to suspicious DNS queries that are detected by Amazon GuardDuty within your Amazon Web Services (AWS) environment. The Security Pillar of the AWS Well-Architected Framework includes incident response, stating that your organization should implement mechanisms to […]