AWS Security Blog
Tag: AWS KMS
Top 2022 AWS data protection service and cryptography tool launches
February 28, 2023: We updated this blog to include AWS Wickr. Given the pace of Amazon Web Services (AWS) innovation, it can be challenging to stay up to date on the latest AWS service and feature launches. AWS provides services and tools to help you protect your data, accounts, and workloads from unauthorized access. AWS […]
How to set up ongoing replication from your third-party secrets manager to AWS Secrets Manager
Secrets managers are a great tool to securely store your secrets and provide access to secret material to a set of individuals, applications, or systems that you trust. Across your environments, you might have multiple secrets managers hosted on different providers, which can increase the complexity of maintaining a consistent operating model for your secrets. […]
How to tune TLS for hybrid post-quantum cryptography with Kyber
January 30, 2024: The API in this blog post has been changed in newer version of the AWS CRT Client. See this page for more info. January 25, 2023: AWS KMS, ACM, Secrets Manager TLS endpoints have been updated to only support NIST’s Round 3 picked KEM, Kyber. s2n-tls and s2n-quic have also been updated […]
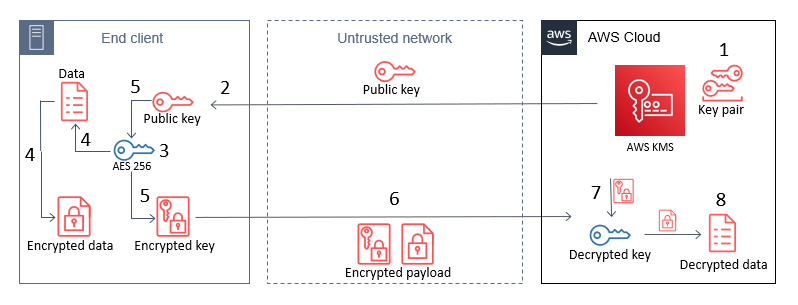
How to use AWS KMS RSA keys for offline encryption
October 28, 2022: This blog post has been updated to reflect that CBC has changed to CTR, as well as a few more modifications. This blog post discusses how you can use AWS Key Management Service (AWS KMS) RSA public keys on end clients or devices and encrypt data, then subsequently decrypt data by using […]
How to protect HMACs inside AWS KMS
April 20, 2022: In the section “Use the HMAC key to encode a signed JWT,” we fixed an error in the code sample. Today AWS Key Management Service (AWS KMS) is introducing new APIs to generate and verify hash-based message authentication codes (HMACs) using the Federal Information Processing Standard (FIPS) 140-2 validated hardware security modules […]
Best practices: Securing your Amazon Location Service resources
Location data is subjected to heavy scrutiny by security experts. Knowing the current position of a person, vehicle, or asset can provide industries with many benefits, whether to understand where a current delivery is, how many people are inside a venue, or to optimize routing for a fleet of vehicles. This blog post explains how […]
Top 2021 AWS Security service launches security professionals should review – Part 1
Given the speed of Amazon Web Services (AWS) innovation, it can sometimes be challenging to keep up with AWS Security service and feature launches. To help you stay current, here’s an overview of some of the most important 2021 AWS Security launches that security professionals should be aware of. This is the first of two […]
How to use tokenization to improve data security and reduce audit scope
April 25, 2023: We’ve updated this blog post to include more security learning resources. Tokenization of sensitive data elements is a hot topic, but you may not know what to tokenize, or even how to determine if tokenization is right for your organization’s business needs. Industries subject to financial, data security, regulatory, or privacy compliance […]
Managing permissions with grants in AWS Key Management Service
August 9, 2022: This post has been updated to correct the references on RDS documentation. February 22, 2022: This post has been updated to clarify details of the example KMS grants provided in this blog. AWS Key Management Service (AWS KMS) helps customers to use encryption to secure their data. When creating a new encrypted […]
How US federal agencies can use AWS to encrypt data at rest and in transit
This post is part of a series about how Amazon Web Services (AWS) can help your US federal agency meet the requirements of the President’s Executive Order on Improving the Nation’s Cybersecurity. You will learn how you can use AWS information security practices to meet the requirement to encrypt your data at rest and in […]