AWS Security Blog
Category: Expert (400)
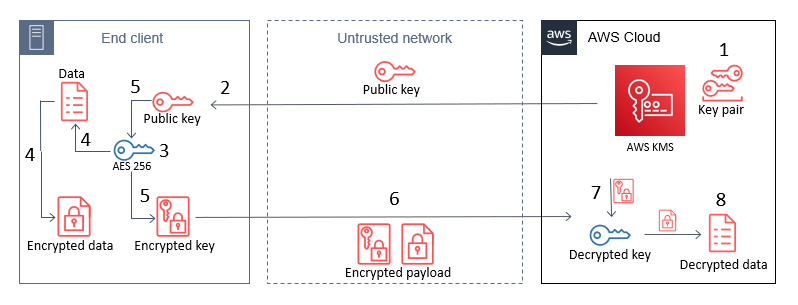
How to use AWS KMS RSA keys for offline encryption
October 28, 2022: This blog post has been updated to reflect that CBC has changed to CTR, as well as a few more modifications. This blog post discusses how you can use AWS Key Management Service (AWS KMS) RSA public keys on end clients or devices and encrypt data, then subsequently decrypt data by using […]
LGPD workbook for AWS customers managing personally identifiable information in Brazil
Portuguese version AWS is pleased to announce the publication of the Brazil General Data Protection Law Workbook. The General Data Protection Law (LGPD) in Brazil was first published on 14 August 2018, and started its applicability on 18 August 2020. Companies that manage personally identifiable information (PII) in Brazil as defined by LGPD will have […]
How to secure API Gateway HTTP endpoints with JWT authorizer
This blog post demonstrates how you can secure Amazon API Gateway HTTP endpoints with JSON web token (JWT) authorizers. Amazon API Gateway helps developers create, publish, and maintain secure APIs at any scale, helping manage thousands of API calls. There are no minimum fees, and you only pay for the API calls you receive. Based […]
Security practices in AWS multi-tenant SaaS environments
Securing software-as-a-service (SaaS) applications is a top priority for all application architects and developers. Doing so in an environment shared by multiple tenants can be even more challenging. Identity frameworks and concepts can take time to understand, and forming tenant isolation in these environments requires deep understanding of different tools and services. While security is […]
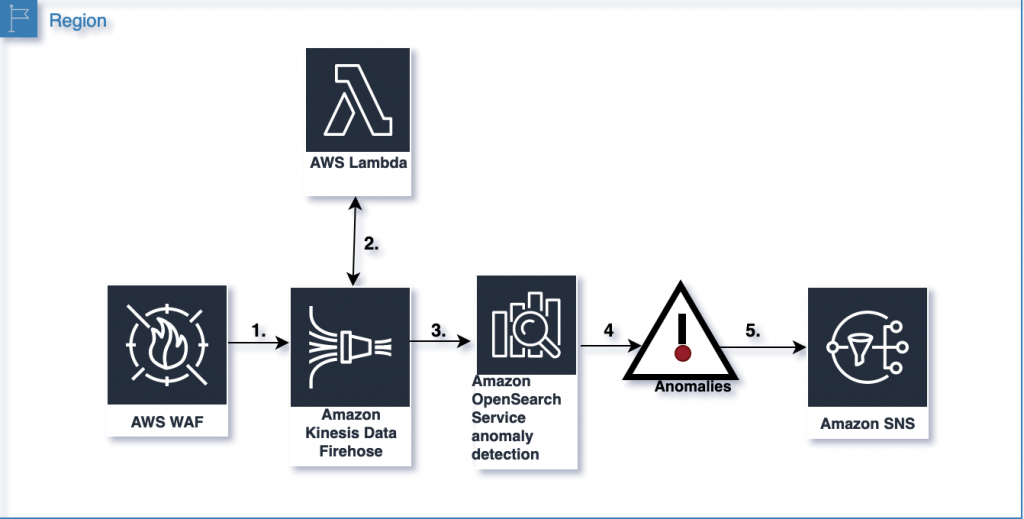
Analyze AWS WAF logs using Amazon OpenSearch Service anomaly detection built on Random Cut Forests
April 23, 2025: We updated the code, screenshots, and narrative. This blog post shows you how to use the machine learning capabilities of Amazon OpenSearch Service to detect and visualize anomalies in AWS WAF logs. AWS WAF logs are streamed to Amazon OpenSearch Service using Amazon Kinesis Data Firehose. Kinesis Data Firehose invokes an AWS […]
Implement OAuth 2.0 device grant flow by using Amazon Cognito and AWS Lambda
In this blog post, you’ll learn how to implement the OAuth 2.0 device authorization grant flow for Amazon Cognito by using AWS Lambda and Amazon DynamoDB. When you implement the OAuth 2.0 authorization framework (RFC 6749) for internet-connected devices with limited input capabilities or that lack a user-friendly browser—such as wearables, smart assistants, video-streaming devices, […]
How to use ACM Private CA for enabling mTLS in AWS App Mesh
Securing east-west traffic in service meshes, such as AWS App Mesh, by using mutual Transport Layer Security (mTLS) adds an additional layer of defense beyond perimeter control. mTLS adds bidirectional peer-to-peer authentication on top of the one-way authentication in normal TLS. This is done by adding a client-side certificate during the TLS handshake, through which […]
Create a portable root CA using AWS CloudHSM and ACM Private CA
March 6, 2025: This post was republished to reference the AWS CloudHSM Client SDK 5 and Amazon Linux 2023 AMI, as well as the new AWS CloudHSM documentation and expiration for the root CA. Feb 17, 2025: This blog post references AWS CloudHSM Client SDK 3, which is no longer the recommended version. AWS recommends […]
How to implement SaaS tenant isolation with ABAC and AWS IAM
April 25, 2023: We’ve updated this blog post to include more security learning resources. August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. Multi-tenant […]
How to verify AWS KMS signatures in decoupled architectures at scale
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. AWS Key Management Service (AWS KMS) makes it easy to create and manage cryptographic keys […]