AWS Security Blog
Category: Developer Tools
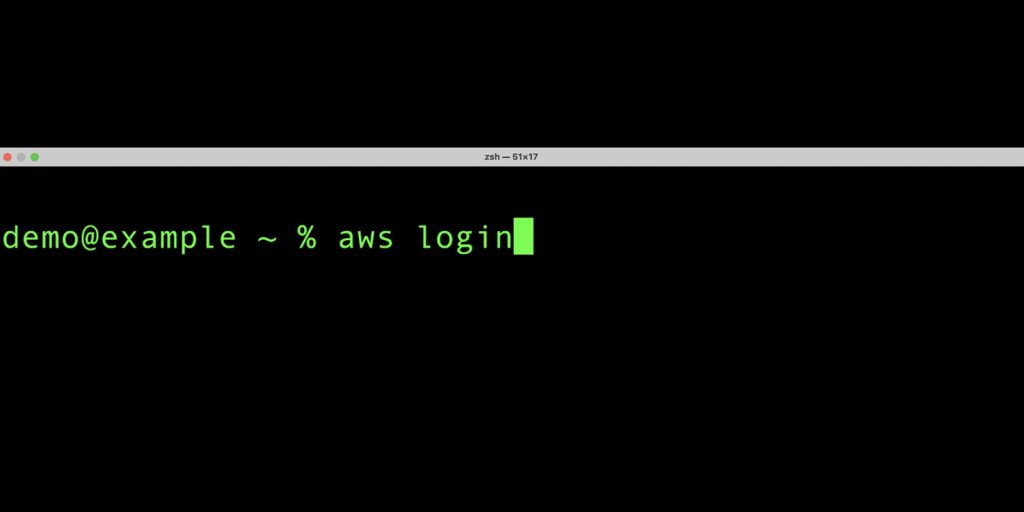
Simplified developer access to AWS with ‘aws login’
Getting credentials for local development with AWS is now simpler and more secure. A new AWS Command Line Interface (AWS CLI) command, aws login, lets you start building immediately after signing up for AWS without creating and managing long-term access keys. You use the same sign-in method you already use for the AWS Management Console. […]
Implementing Defense-in-Depth Security for AWS CodeBuild Pipelines
Recent security research has highlighted the importance of CI/CD pipeline configurations, as documented in AWS Security Bulletin AWS-2025-016. This post pulls together existing guidance and recommendations into one guide. Continuous integration and continuous deployment (CI/CD) practices help development teams deliver software efficiently and reliably. AWS CodeBuild provides managed build services that integrate with source code […]
Strengthen the DevOps pipeline and protect data with AWS Secrets Manager, AWS KMS, and AWS Certificate Manager
In this blog post, we delve into using Amazon Web Services (AWS) data protection services such as AWS Secrets Manager, AWS Key Management Service (AWS KMS), and AWS Certificate Manager (ACM) to help fortify both the security of the pipeline and security in the pipeline. We explore how these services contribute to the overall security […]
Automate Cedar policy validation with AWS developer tools
Cedar is an open-source language that you can use to write policies and make authorization decisions based on those policies. AWS security services including AWS Verified Access and Amazon Verified Permissions use Cedar to define policies. Cedar supports schema declaration for the structure of entity types in those policies and policy validation with that schema. […]
Best Practices to help secure your container image build pipeline by using AWS Signer
AWS Signer is a fully managed code-signing service to help ensure the trust and integrity of your code. It helps you verify that the code comes from a trusted source and that an unauthorized party has not accessed it. AWS Signer manages code signing certificates and public and private keys, which can reduce the overhead […]
Access token security for microservice APIs on Amazon EKS
In this blog post, I demonstrate how to implement service-to-service authorization using OAuth 2.0 access tokens for microservice APIs hosted on Amazon Elastic Kubernetes Service (Amazon EKS). A common use case for OAuth 2.0 access tokens is to facilitate user authorization to a public facing application. Access tokens can also be used to identify and […]
Mitigate data leakage through the use of AppStream 2.0 and end-to-end auditing
Customers want to use AWS services to operate on their most sensitive data, but they want to make sure that only the right people have access to that data. Even when the right people are accessing data, customers want to account for what actions those users took while accessing the data. In this post, we […]
Use new account assignment APIs for AWS SSO to automate multi-account access
September 28, 2022: In July 2022, we renamed AWS Single Sign-On to AWS IAM Identity Center. In this blog, you will notice that we preserved backward compatibility with API calls and CLI scripts by retaining the API and CLI namespaces that were used under AWS Single Sign-On. September 12, 2022: This blog post has been […]
Enhance programmatic access for IAM users using a YubiKey for multi-factor authentication
Organizations are increasingly providing access to corporate resources from employee laptops and are required to apply the correct permissions to these computing devices to make sure that secrets and sensitive data are adequately protected. The combination of Amazon Web Services (AWS) long-term credentials and a YubiKey security token for multi-factor authentication (MFA) is an option […]
Isolating network access to your AWS Cloud9 environments
In this post, I show you how to create isolated AWS Cloud9 environments for your developers without requiring ingress (inbound) access from the internet. I also walk you through optional steps to further isolate your AWS Cloud9 environment by removing egress (outbound) access. Until recently, AWS Cloud9 required you to allow ingress Secure Shell (SSH) […]